Basic Usage: Introduction to the workbench
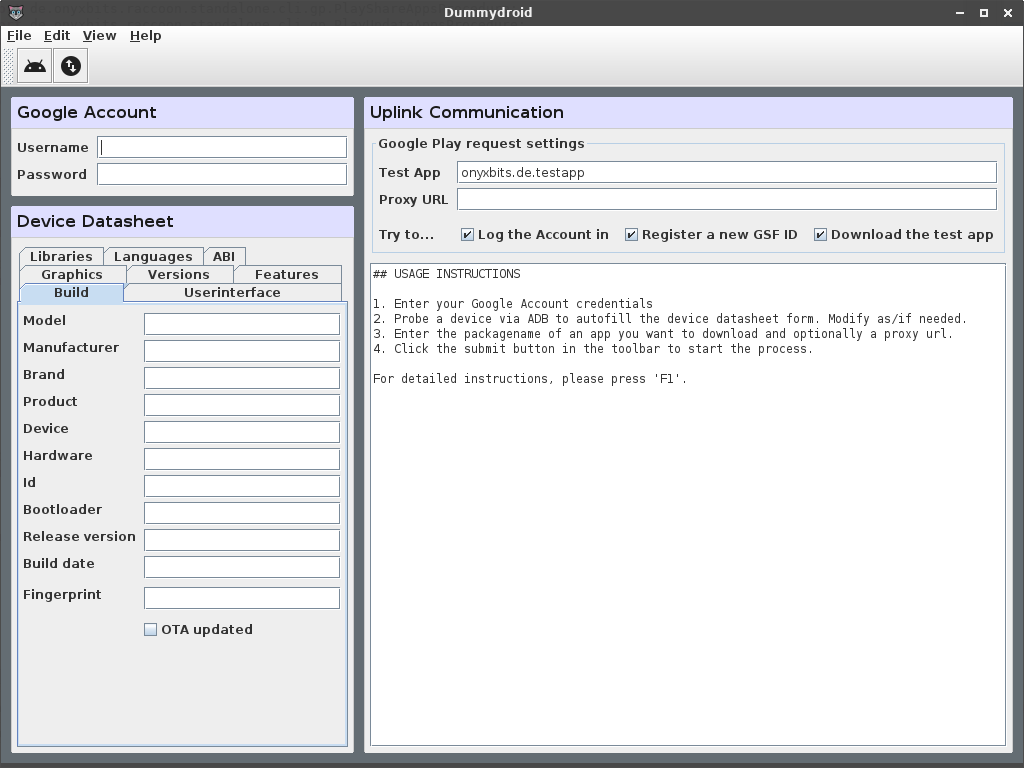
When you open DummyDroid, you will be greeted by the workbench. The two small boxes on the left hand side models a pseudo Android device, the large box on the right, its communication with Google Play.
While the workbench may seem a bit daunting at first, it really is just all about answering a simple question:
Which device is an app compatible with and is a given proxy going to help me bypass a geo blocks?
The “Google Account” box
Google Play cannot be accessed anonymously. It is recommended to use a throw away account when experimenting with DummyDroid. Even if you have a valid account, you might be prevented from logging in for two reasons:
- The account in question has two factor auth enabled (DummyDroid does not handle that).
- Google has never seen you logging in with this device (duh!) from your current IP address and thinks that your account might have been stolen (you’ll also get a security alert via email).
In both cases you need to log in with your webbrowser. Disable 2FA in the first case and confirm that the logging attempt was really from you in the second.
The credentials you enter will be used to request an auth token, if the login action (see below) is selected. This replaces your password when communicating with Play. You can check/set the Auth token via ☰ View > Auth Token .
The “Device Datasheet” box
The datasheet contains what Google wants to know about your device in order to determine whether or not an app is compatible with it (and hence to decide whether or not you are allowed to download it).
The recommended way to fill this form is by either using ☰ Edit > Probe Device to scan a device, connected by USB cable or to paste a JSON specification via ☰ Edit > Paste Device Specification , then make manual adjustments as needed.
To probe devices, ADB must be installed and running. If you want to use a system wide ADB installation, make sure, the daemon is running before clicking the probe button. Otherwise, DummyDroid will offer you to download the software to it’s instance directory and run it from there (the instance directory can be found via the ☰ Help > About dialog).
Note that some devices may only get probed partially. Refer to the Building the datasheet manually section for details.
The “Uplink Communication” box
This box consists of two parts. The upper portion configures the ☰ File > Submit action. The text field in the lower portion shows the progress log.
- Test app
- The packagename of the app, DummyDroid is suppose to download.
- Proxy url
- Optional url of a proxy server to use. See [Using proxies](/dummydroid-v2/using-proxies) for details.
- Log the account in
- If checked, DummyDroid will log the account in and open a new session, represented by an auth token. The auth token is not shown in the workbench, but can be checked/set via ☰ View > Auth Token . As long as DummyDroid has a valid session stored, it does not need to log in again.
- Register a new GSF ID
- If checked, DummyDroid will upload the datasheet and register a new GSF ID. The GSF ID represents the account and the device combination. Much like the auth cookie, it is not shown in the workbench, but can be checked via ☰ View GSF ID . It can also be used for subsequent requests as long as the datasheet is not altered.
- Download the test app
- If checked, DummyDroid will attempt to "download" the test app. No files will be transferred, though (that's the job of Raccoon, after all!). Instead, DummyDroid will just log the urls.
 English
English
 Deutsch
Deutsch